No audio available for this content.
Jamming Signals Criminal Activity in Intermodal Ports
By Logan Scott
More than 25 million containers pass through U.S. intermodal ports every year, with port operations valued at more than $1 billion per day. Measured in 20-foot equivalent units (TEU), the World Bank reports that worldwide, more than 600 million TEU passed through intermodal ports in 2012: 155 million through Chinese ports, 95 million through the EU ports and 43 million through U.S. ports.
The Port of Long Beach alone handled 6,820,806 TEU in 2014. GPS is a central component of automated port operations, but because GPS is widely used in asset tracking and monitoring, it has also become a target for denial-of-service attacks. If we look to the history of computer security, the initial attacks were mostly nuisances, but as criminals figured out how to monetize attacks, the attacks became more damaging, more sophisticated and more profitable.
In January, the U.S. Coast Guard held a public meeting on Maritime Cybersecurity Standards at Department of Transportation headquarters in Washington, D.C. Brett Rouzer, chief of Maritime Critical Infrastructure and Key Resources Protection, Coast Guard Cyber Command, described how a major East Coast intermodal shipping facility was degraded by a GPS disruption for more than seven hours. Two ship-to-shore cranes ceased operation due to loss of position, and two others were degraded. Ports are highly automated; ship-to-shore cranes are just one of the container-handling systems critically reliant on GPS. Fully automated ports providing services for unmanned container ships, trucks and trains lie within the realm of feasibility in the near future.
Rouzer did not specify the motivates for the disruption, how the attack was mounted, or if the shipping facility was even the intended target of the attack (I suspect it was not). Jamming is not a highly selective process, and it can affect numerous unintended targets.
In June 2014, I reported to the PNT Advisory Board on how every third or fourth truck on Highway 30B near Portland (Oregon) International Airport was radiating at or near the GPS L1 frequency. This highway leads to several nearby Port of Portland intermodal terminals west of the airport. The Federal Bureau of Investigation recently reported that “In 46 reported incidents, the thieves placed one or more GPS jammers in cargo containers with stolen automobiles” (italics mine). High-end automobiles command premium prices in foreign markets and are stolen and shipped out of the country within hours, usually via intermodal container. Active jammers can affect not only the automobile’s GPS tracker, but also trackers on other containers, ship’s navigation systems, straddle carriers and ship-to-shore cranes. Again, jamming is not selective.
Of particular note as cited above, criminals are beginning to use multiple jammers. Car theft rings are not unique in this. According to the Pharmaceutical Cargo Security Coalition in July 2014, “a tractor and trailer hauling $2 million worth of pharmaceutical products was stolen from a truck stop in Cartersville, Georgia, with the thieves deploying two separate GSM jammers.” The criminal’s motivation is that tracking devices can be hard to find and disable; just because you found one doesn’t mean that there isn’t another. The use of multiple jammers in criminal enterprise is indicative of a threat escalation where bad actors are seeking higher effect. This could lead to higher jamming powers and so on; and also more collateral damage.
Response
What is a correct and measured response to threats against navigation and timing? The key is to be on the lookout for emerging threats and to have a flexible response. Early detection usually yields a more effective and lower cost response; witness Ebola and ISIS. Following a public health model would seem to offer better prospects for protecting access to PNT. To this end, I would argue that situational awareness is the first important step.
One of the most striking comments that Sarah Mahmood (DHS) made at last June’s PNT Advisory Board meeting was about how backup systems are often not activated or used because the GPS receiver fails to recognize that there is a problem. As we move towards resilient PNT architectures, one of the most critical needs is to be able to distinguish good signals from bad signals and act accordingly.
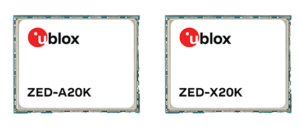
Most GNSS receivers already have fairly advanced jamming detection capabilities by virtue of having an automatic gain control. Sudden changes in precorrelation input power levels are not normal and can indicate jamming or RF spoofing. Many GNSS receivers, particularly those that go into embedded mobile applications, also have sophisticated spectrum- and temporal-analysis capabilities, used mainly for diagnostic purposes in looking for interference sources from other components of the device. This same capability can be used in detecting and fingerprinting jammers. We already have the smoke alarms; we must amplify their use and visibility to the wider community of GNSS users and beyond.
Detection
One notable aspect of the port incident was the duration: more than seven hours. Rapidly finding and disabling the jammer was clearly a problem in this case. The old adage is that to find a stationary source (jammer) you need to be moving, and to find a moving source, you need to be stationary. Trucks and trains entering or leaving a port all pass through gates that can act as a simple chokepoint for detecting and finding active jammers. Properly hardened ship-to-shore cranes and straddle carriers can also act as a chokepoint. Straddle carriers used in moving containers around the yard and between modes could be very good at finding stationary jammers.
There are numerous relatively low-cost approaches for finding jammers in support of enforcement actions. One additional point: law enforcement officials need to be better educated as to why they should be interested in jammers; jammers point towards a crime much like smoke points to a fire.
Given the economic criticality of port operations and the concentration of assets (and asset trackers), we may see increased incidence of GPS disruptions. The situation is not critical yet, but it does bear watching. If jamming events increase or it takes too long to find and disable jammers, improved operational resilience will be needed.
Inertial measurement units are already used in many critical applications, but they don’t offer long-duration capability. They drift. Using adaptive arrays in critical equipments is another possibility, but they are not a panacea. Adaptive arrays are physically large, and standard null-steering approaches are not compatible with RTK processing. Precise positioning systems based on GNSS require specialized antenna-receiver designs to achieve a high level of jam resistance.
While I strongly believe eLoran is an urgently needed augmentation for resilient wide area navigation, it is not capable of the centimeter-level precision required for machine control, for example ship-to-shore cranes and straddle carriers.
High-precision local-area positioning systems based on optical systems, RFID and/or Locata-style systems may be the best approach for creating a defense in depth.
And then there is the cybersecurity question, which I will leave for another day.
Note: A video of the Coast Guard meeting is on YouTube. Rouzer’s talk starts at 36:30, with the port jamming incident mentioned at 48:51.
Logan Scott has 35 years of military and civil GPS systems engineering experience. He is a consultant specializing in radio frequency signal processing and waveform design. At Texas Instruments, he pioneered approaches for building high-performance, jamming-resistant digital receivers. He is a co-founder of Lonestar Aerospace, an advanced decision analytics company in Texas. Logan is a Fellow of the Institute of Navigation and holds 37 U.S. patents.












John Lavrakas
Great article, Logan. I appreciate the directness and practical nature of your comments and recommendations. A thought: would it not make sense for federal agencies to use the jammers to locate the illegal property (stolen high end vehicles for example) and then to message out the great convenience the jammers make in locating this property. This message might cause the malefactors to think twice about using jammers to protect their cargo, recognizing that in fact it leads authorities right to it. A form of reverse psychology. Just a thought.